A Comprehensive Guide to Implementing CIEM

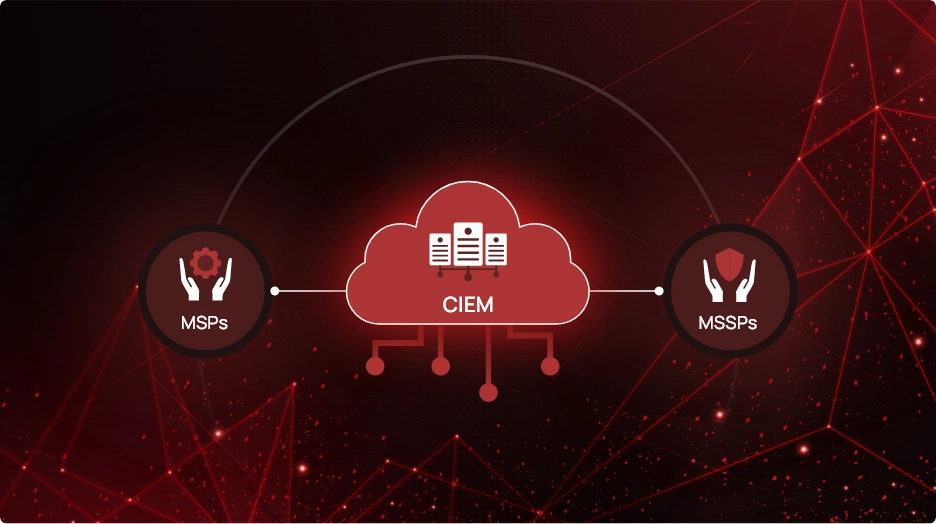
Cloud Infrastructure Entitlement Management (CIEM) plays a vital role in ensuring the security of cloud environments by managing identities and their access rights. As organizations increasingly move their applications to the cloud, the importance of CIEM has grown significantly. Implementing CIEM can be complex, and many organizations may struggle without proper guidance.
Understanding CIEM
Cloud Infrastructure Entitlement Management (CIEM) is a critical aspect of cloud security, particularly in modern cloud environments where traditional network boundaries are eliminated. CIEM focuses on managing identities and their entitlements within cloud systems.
In simpler terms, CIEM ensures that the right people or systems have the appropriate level of access to resources in the cloud. It helps organizations effectively manage permissions, ensuring that only authorized users can access sensitive data or perform specific actions.
CIEM solutions provide visibility into cloud identities and their entitlements, allowing organizations to monitor and control access effectively. This visibility is crucial in addressing the challenges posed by the dynamic nature of cloud environments, where identities and permissions can change rapidly.
Organizations need CIEM solutions to mitigate risks associated with unauthorized access, privilege escalation, and data breaches. CIEM also helps organizations address cloud compliance monitoring requirements, enhance security posture, and improve overall operational efficiency in the cloud.
Researching Different Components of CIEM
When considering the implementation of CIEM, it’s essential to research and understand the different components of CIEM solutions available in the market. With CIEM, cloud solutions come in various forms, each catering to specific aspects of cloud identity and access management. Three primary types include:
- Role entitlement management: Ensures that users are assigned appropriate roles based on their responsibilities and access requirements.
- Application entitlements: Allows organizations to control access to sensitive data and functionalities within their applications.
- Identity lifecycle management: Includes provisioning, deprovisioning, and managing access rights throughout the user’s journey within the organization.
Prioritizing Security in CIEM Implementation
Security breaches in cloud environments can lead to significant data loss and compromise organizational integrity. Organizations should consider implementing the following security measures:
- Two-Factor Authentication (2FA): Enabling 2FA adds an extra layer of security by requiring users to provide two forms of identification before accessing the CIEM system. This significantly reduces the risk of unauthorized access, enhancing overall security.
- Data encryption: Encrypting data stored on cloud servers ensures that even if unauthorized access occurs, the data remains unreadable and unusable to unauthorized parties. This mitigates the risk of data breaches and protects sensitive information from being compromised.
- Access control: Limiting data access to only authorized personnel helps prevent unauthorized individuals from tampering with permissions and entitlements. Implementing strict access control measures ensures that sensitive data remains protected at all times.
Testing and Troubleshooting CIEM
Testing allows organizations to validate the functionality of the CIEM solution and ensure that it meets their security requirements. It helps identify any bugs, glitches, or vulnerabilities that may exist within the system, allowing for timely remediation.
Troubleshooting involves diagnosing and resolving any issues or errors that arise during the CIEM implementation process. It requires careful investigation and analysis to identify the root cause of the problem and implement appropriate solutions.
Some tips for effective testing and troubleshooting in CIEM implementation include:
- Conducting regular performance assessments using tools such as load testing and stress testing to evaluate the scalability and reliability of the CIEM solution.
- Keeping track of usage metrics, such as logins and failed attempts, to identify any unusual patterns or suspicious activities that may indicate potential security threats.
- Maintaining backups of data to ensure that critical information is protected in the event of an emergency or system failure.
Planning and Preparation for CIEM Implementation
Proper planning helps organizations identify potential challenges and risks upfront, allowing them to develop effective strategies for addressing them.
Planning and preparation tips before CIEM implementation:
- Conduct a comprehensive analysis of the organization’s cloud environment
- Identify existing identities, permissions, and access controls
- Assess organizational needs and goals with regard to CIEM
- Determine which types of applications will be moved to the cloud
- Identify specific security requirements
- Consult with internal stakeholders and external experts, if necessary, to gather insights and perspectives on the organization’s CIEM implementation strategy.
- Develop a detailed timeline and roadmap for the implementation process
- Outline key milestones, tasks, and responsibilities
Avoid Rushing the Implementation Process
Rushing through the CIEM implementation process can lead to oversights, errors, and potential security vulnerabilities. It’s essential to prioritize tasks, seek assistance if needed, and conduct thorough testing to ensure a successful implementation.
Work With a Team of Experts
Collaborating with an experienced team during CIEM implementation is crucial for ensuring a successful outcome. Experienced teams bring valuable insights, knowledge, and expertise to the table, helping organizations navigate the complexities of CIEM implementation effectively. When choosing the right team of experts, organizations should consider factors such as:
Industry experience: Look for a team with extensive experience in CIEM implementation within your specific industry. Industry-specific knowledge allows a team to understand unique challenges and requirements, ensuring a tailored approach to CIEM implementation.
Knowledge and skills: Ensure that the team possesses the necessary knowledge and skills to handle all aspects of CIEM implementation, from planning and deployment to troubleshooting and support. Look for certifications and credentials that demonstrate expertise in cloud security and CIEM solutions.
CheckRed offers expertise in CIEM, with a team of seasoned professionals dedicated to helping organizations achieve their security objectives. With CheckRed’s CIEM capabilities, organizations get access to various features like cloud compliance tools and cloud privileged access management. Organizations can benefit from comprehensive support throughout the CIEM implementation process, ensuring a smooth and successful transition to a secure cloud environment.