Guided Remediation
As organizations worldwide rely on SaaS applications to run their business operations, they have embraced the identification, mitigation, and even prevention of security risks. SaaS security posture management is growing in importance across industries. However, as application usage increases, efficiently monitoring the SaaS environment becomes critical.
Ensuring that each SaaS application is configured as per organizational needs and managing an array of third-party integrations is usually done manually by most security teams. This can often be quite tedious, leading to missed alerts or delayed mitigation efforts.
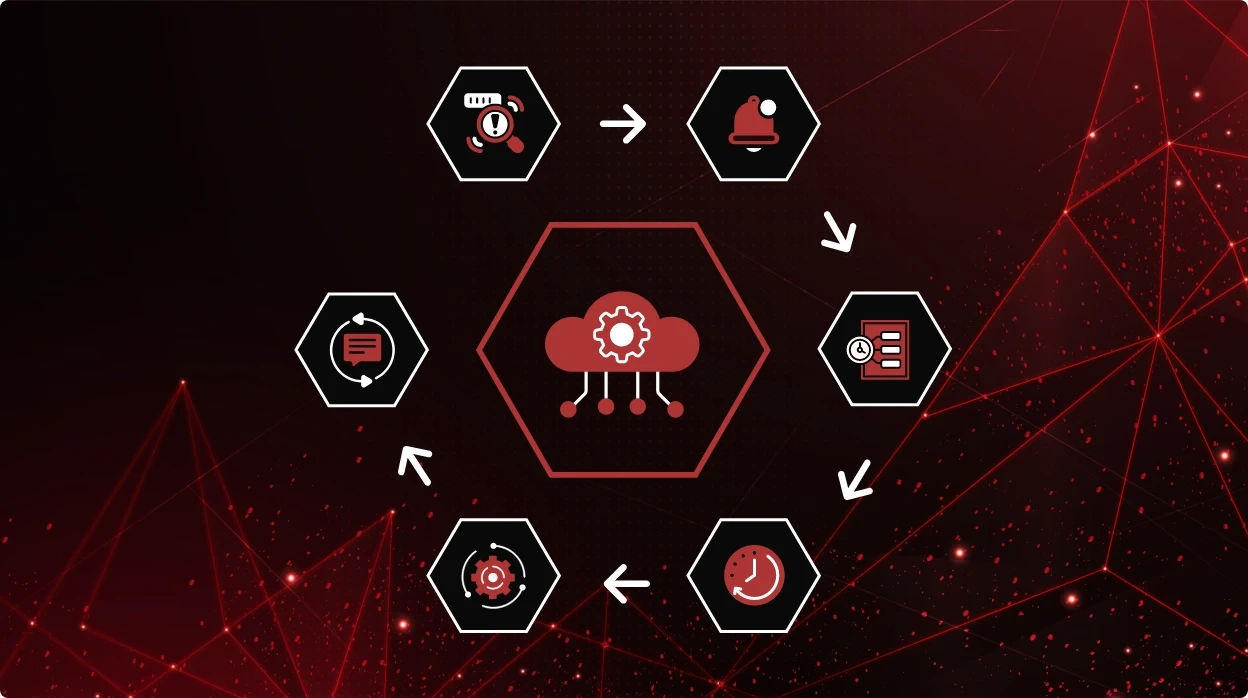
Custom alerts and guided remediation workflows are powerful tools to help organizations improve their SaaS security posture. They can be set up to monitor for potential risks continuously and alert analysts when misconfigurations are detected. This capability helps reduce the risk of costly data breaches by providing faster response times and better visibility. Additionally, it allows teams to respond quickly to incidents before they become major problems, saving time and money as well as improving overall security posture.
Why security teams need guided remediation
Guided remediation workflows are a critical component of an effective SaaS security strategy. Guided remediation provides contextual visibility, risk analytics, and step-by-step measures to resolve security risks. It helps reduce manual intervention, support security teams, and strengthen SaaS security posture. Benefits of guided remediation workflows include:
- Consistent response to security incidents: By having a predefined set of steps for responding to security incidents, organizations can ensure that risks are mitigated in a consistent and thorough manner. This can help prevent incidents from being overlooked or mishandled.
- Reduced response time: A guided remediation workflow helps security teams respond to incidents faster. By streamlining the response process, organizations can reduce the severity and impact of security incidents and prevent them from escalating.
- Automated responses: Remediation workflows can be automated to some degree, which can help reduce the workload of security teams. For example, certain types of minor security incidents may be resolved automatically without the need for human intervention.
- Improved communication: Remediation workflows can also help improve communication internally within the organization. By clearly defining roles and responsibilities for different teams, security incidents can be handled seamlessly.
- Better documentation: Remediation workflows can be used to document the response process, providing a record of what actions were taken during a security incident. This can be useful for auditing purposes or for identifying areas for improvement in the incident response process.
The case for custom security alerts
Each organization generally has its own SaaS application configurations and policies, resulting in a high volume of security alerts. In many instances, contextual intelligence is not available, leading to alert fatigue and delayed response times. When context is added to each alert and customized as per internal policies, security teams are more equipped to respond to risks.
Custom alerts help organizations in several ways, including:
- Early detection of security threats
- Specific notifications based on the nature of the security threat
- Prioritization of security team response
- Reduced time to resolution for security incidents
For instance, custom alerts can be set up to monitor unauthorized access to sensitive data stored on the cloud, enabling immediate action to prevent any potential damage. Similarly, monitoring for suspicious login attempts can alert the security team to a potential attack and enable them to take action before any damage is done.
Implementing custom alerts and guided remediation
Implementing custom alerts and guided remediation workflows is crucial for enhancing an organization’s SaaS security posture. Here are some key points to keep in mind:
- Identify critical assets and define appropriate alerts for each asset
- Configure alerts to be specific and prioritize them according to their severity
- Test alerts and remediation workflows regularly to ensure proper functioning
- Train employees on how to respond to alerts and remediate vulnerabilities
- Regularly review and update custom alerts and remediation workflows to ensure efficiency
- Automate remediation workflows to take corrective action if an alert is triggered
By implementing custom alerts and remediation workflows, organizations can reduce the impact of security issues and response time and stay ahead of evolving security threats. CheckRed’s SSPM and CSPM platform can be customized to meet your organizational policies and delivers automated and semi-automated remediation workflows, allowing you to prioritize what matters most.


