Identity and Access Management
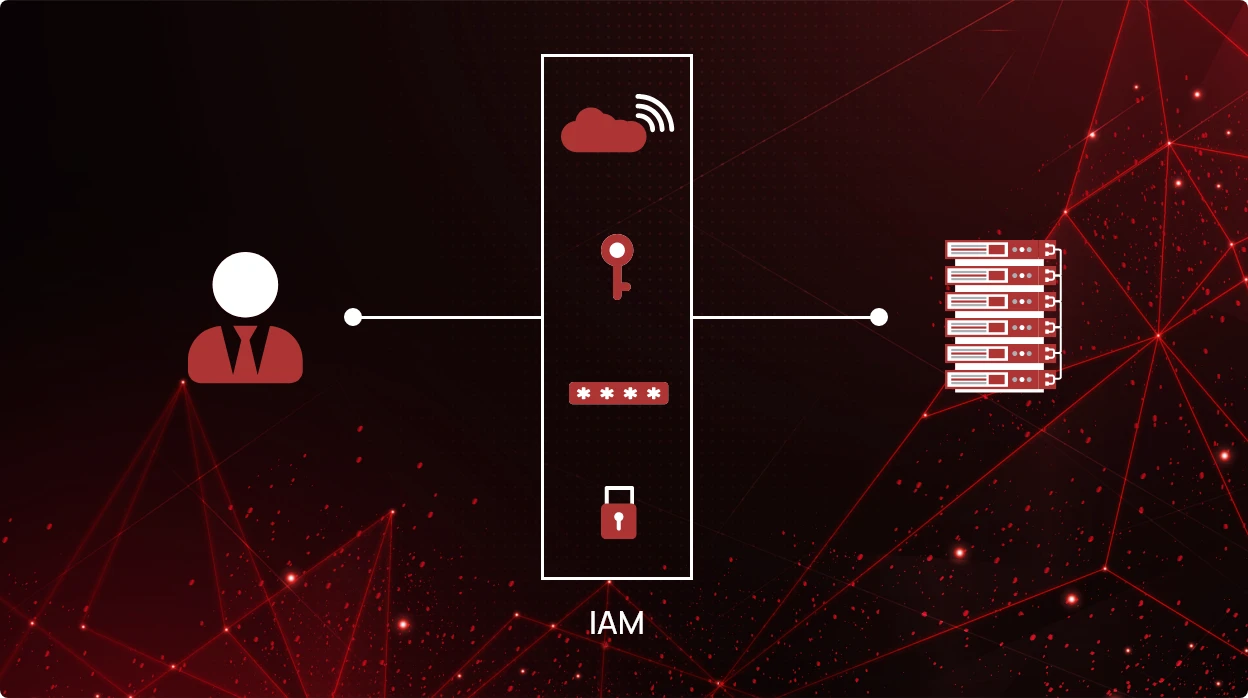
Safeguarding sensitive data and ensuring secure access to resources is of the utmost importance for any business. This is where the need for Identity and Access Management (IAM) arises. IAM encompasses the policies, technologies, and processes that allow businesses to control user access to their data. It encompasses user authentication, authorization, and privilege management.
The demand for reliable IAM solutions has never been more pressing due to the increasing usage of Software-as-a-Service (SaaS) and cloud environments, where data and applications live outside of conventional network perimeters. The dangers and difficulties posed by data breaches, insider threats, compliance standards, and the complexity of regulating user access must be addressed by organizations. They can improve security, optimize user provisioning, and guarantee compliance by deploying efficient IAM techniques.
Understanding the role of IAM in SaaS and cloud environments
IAM plays a pivotal role in ensuring secure and controlled access to resources. In cloud computing, IAM provides centralized user authentication and authorization, acting as a gatekeeper for accessing various applications and services. It verifies user identities, manages credentials, and enforces access policies to protect sensitive data. Additionally, IAM enables granular access control and privilege management, granting users appropriate levels of permissions based on their roles and responsibilities.
In SaaS environments, IAM takes on additional responsibilities. It encompasses user provisioning and lifecycle management, simplifying the onboarding and offboarding processes. Single Sign-On (SSO) functionality ensures seamless access to multiple SaaS applications with a single set of credentials, improving user experience and productivity. Role-Based Access Control (RBAC) allows organizations to define and manage user roles, streamlining access management by assigning permissions based on job functions.
By understanding the role of IAM in cloud and SaaS environments, organizations can effectively secure their resources, enforce access policies, and optimize user management processes.
Risks and challenges in IAM for SaaS and cloud environments
Implementing IAM in SaaS and cloud environments brings several security risks and challenges that organizations must address to ensure robust security and compliance. Here are some key areas of concern:
Data breaches and unauthorized access
- The exposure of sensitive data due to weak access controls or compromised credentials poses a significant threat.
- Unauthorized access can result in data breaches, financial loss, reputational damage, and legal consequences.
Insider threats and privilege abuse
- Insiders with legitimate access may misuse their privileges, intentionally or unintentionally, leading to data leaks or unauthorized modifications.
- Organizations must monitor user activity and implement controls to detect and mitigate insider threats.
Lack of visibility and control over user access
- Organizations may struggle to have clear visibility into who has access to what resources, making it challenging to identify and address security gaps.
- Managing user access across multiple SaaS and cloud applications can be complex and prone to errors.
Compliance and regulatory requirements
- Organizations need to adhere to various compliance and regulatory standards, such as GDPR or HIPAA, which require strict control over access to sensitive data.
- IAM solutions must enable organizations to enforce access controls and provide audit trails for compliance reporting.
Scalability and complexity of IAM deployments
- As organizations grow and adopt more SaaS and cloud services, managing user identities and access permissions becomes more complex.
- IAM systems should be scalable to handle increasing user volumes and adaptable to changing business needs.
To mitigate these risks and challenges, organizations must invest in comprehensive IAM solutions that offer robust access controls, continuous monitoring, and automation capabilities. By implementing IAM best practices, organizations can strengthen security, enhance compliance, and streamline user access management in SaaS and cloud environments.
Harnessing CheckRed for enhanced SSPM and CSPM in SaaS and cloud environments
CheckRed revolutionizes SSPM and CSPM, delivering comprehensive capabilities to enhance security posture. The platform optimizes access privileges based on the principle of least privilege and offers RBAC optimization, streamlining user roles and permissions management.
With CheckRed, organizations experience streamlined configuration and compliance, enhanced visibility and control, proactive security, and efficient privilege management, bolstering the overall security posture of their SaaS and cloud environments.