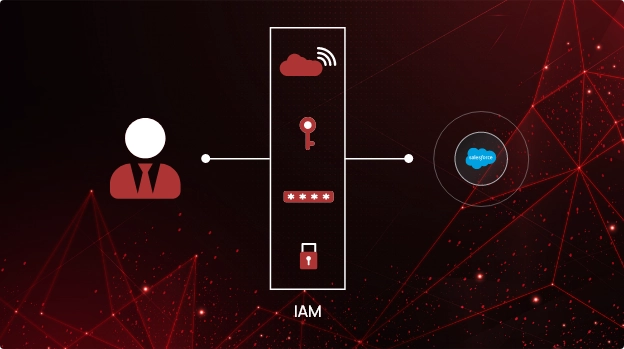
Improve Identity and Access Management Within Salesforce
Organizations across industries use a CRM (Customer Relationship Management) tool for their sales and marketing operations, and Salesforce is one of the most popular tools thanks to its user-friendly interface and customizable features. Its cloud-based architecture allows users to access critical business data from anywhere. However, the data sharing feature can lead to inadvertent exposure of sensitive data to third-parties, partners, or even the public!
Effective Identity and Access Management (IAM) is crucial for securing your Salesforce environment. However, managing access controls and identifying inactive accounts can be challenging. With a SaaS security posture management (SSPM) tool like CheckRed, it becomes easy to implement identity-based access and user privileges. Catching inconsistencies in user behavior and mitigating the risk of data breaches has never been easier.
User roles and permissions in Salesforce
There are multiple identity and access configurations possible within the Salesforce environment for individual users and groups of users. It allows you to define and control different types of users and what access levels or privileges each of them require. But as users and databases increase, it is difficult to track each and every one and have a complete overview of how data is shared.
- At the object level (or database table level), you can define user access and privileges including permissions to view, create, modify, or even delete.
- You can also manage access levels at the field level (one particular data point). For instance, a user can modify only some fields within an object.
- When it comes to the record level, Salesforce provides multiple access roles and user privileges including read-only settings, role hierarchies, sharing rules, and restrictions.
Organizations share data with their own employees, third-party vendors, partners, and others. Each user or user group within Salesforce requires a robust IAM system to manage user roles and privileges.
How does an SSPM tool help?
| Identification of Security Risks | Reduction in Costs | Compliance with Regulatory Requirements |
|---|---|---|
| The tool enables quick identification of security risks related to misconfiguration of data and user access. This ensures that your organization is always secure and protected. | A comprehensive SSPM solution helps reduce the costs associated with managing your Salesforce environment by eliminating unnecessary access and streamlining access management processes. | Compliance with various regulatory requirements, such as HIPAA, GDPR, and SOC 2, is achieved by enforcing strong access controls and auditing capabilities, avoiding costly penalties. |
Here’s what CheckRed offers:
Let’s take a look at the capabilities CheckRed offers to help you enhance your Salesforce application’s security posture.
Real-time risk detection
CheckRed uses rule sets and templates to monitor application activities and breaches in real-time, identifying anomalies and security breaches promptly.
Centralized dashboard
CheckRed’s centralized dashboard provides real-time visibility into your Salesforce environment, helping security teams quickly identify and address risks.
Prioritizing key misconfigurations
Automated notifications streamline response processes, and alerts are classified based on criticality and risk scoring for efficient prioritization.
Customized remediation workflows
CheckRed delivers action-driven alerts and personalized suggestions for quick issue resolution. Tracking alerts from detection to resolution ensures continuous improvement.
On-demand analytics
CheckRed’s on-demand analytics and customized reports ensure compliance with industry standards and provide a comprehensive overview of Salesforce security.
Respond efficiently to identity misconfigurations in Salesforce
Ensure seamless Salesforce SaaS security posture management with comprehensive identity and access management for all users! Get a clear, consolidated view of user accounts, permissions, and privileged activities to eliminate any weak spots. With CheckRed, you gain an unbeatable combination of visibility and control to fortify your security like never before.


