Cloud breaches rarely start with advanced exploits or unknown vulnerabilities. Most begin with something far more ordinary:...
How a Stolen SSO Login Led to Millions of Records Exposed in Retail
When news broke that Panera Bread had suffered a major data breach impacting more than five million customers, the...
Betterment Data Breach: Why Unauthorized Access Is a Major Fintech Risk
When Betterment disclosed unauthorized access to parts of its systems in January, the company emphasized that customer...
RBI’s .bank.in Mandate: A New Trust Anchor for Digital Banking — and Why It’s Only the Beginning
India’s banking system is undergoing a critical shift in how digital trust is established. With the rise of phishing,...
Why Cloud and SaaS Misconfigurations Remain a Leading Cause of Data Exposure
Cloud and SaaS platforms have become the backbone of modern business, quietly managing vast volumes of sensitive data...
7 Cloud Security Lessons from the AWS Crypto Mining Campaign
Cloud security incidents are often explained as the result of sophisticated hacks or unknown vulnerabilities. In reality,...
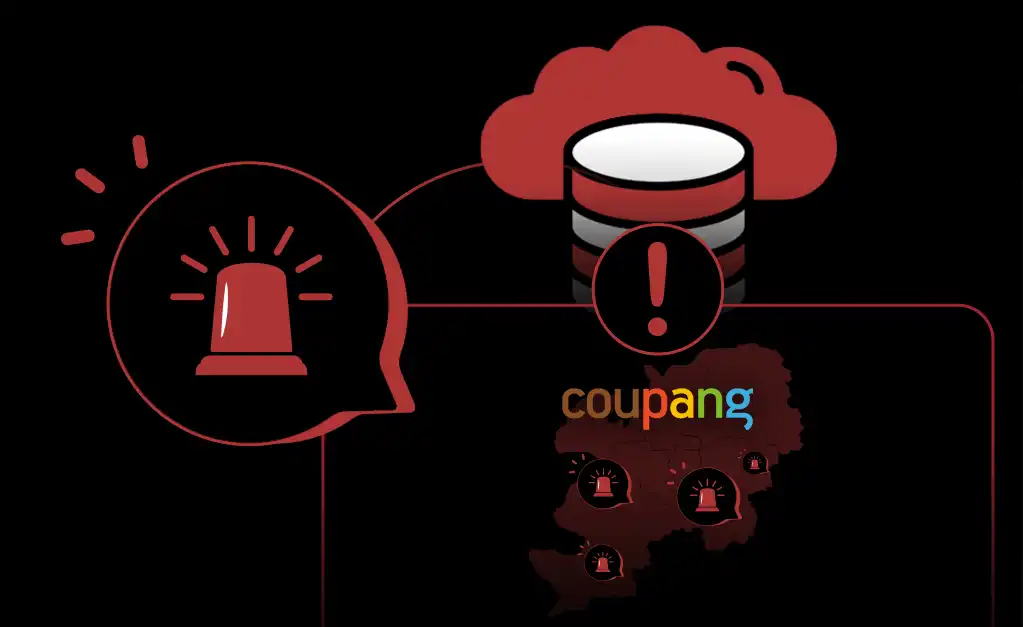
When a Data Breach Becomes a National-Scale Risk
Large data breaches are often framed as corporate failures—an unfortunate but contained problem for a single company to...
Why DNS TXT Records Deserve Governance in Security Programs
DNS TXT records play a critical role in modern cloud environments. They underpin email authentication, domain ownership...
5 Misconfigurations Hackers Hope Retailers Never Fix
If hackers had a holiday wish list, these five misconfigurations would be right at the top. And as the recent Petco...